I’m a passionate writer who loves exploring ideas, sharing stories, and connecting with readers through meaningful content.I’m dedicated to sharing insights and stories that make readers think, feel, and discover something new.
Introduction to AI-Driven Phishing
In a groundbreaking study, researchers have leveraged artificial intelligence to design the most sophisticated phishing plot ever seen. This experiment, conducted to understand the vulnerabilities in current cybersecurity frameworks, has yielded results that are both fascinating and alarming.
The Experiment
The research team employed advanced AI algorithms to simulate human behavior and craft phishing emails that were nearly indistinguishable from legitimate communications. The AI analyzed thousands of phishing attempts, learning from past mistakes to create a seemingly perfect deception.
These emails were then sent to a controlled group of participants, with the aim of assessing the effectiveness of AI-generated phishing. The results were startling, with a significant percentage of recipients falling prey to the scam.
Why AI-Driven Phishing is So Effective
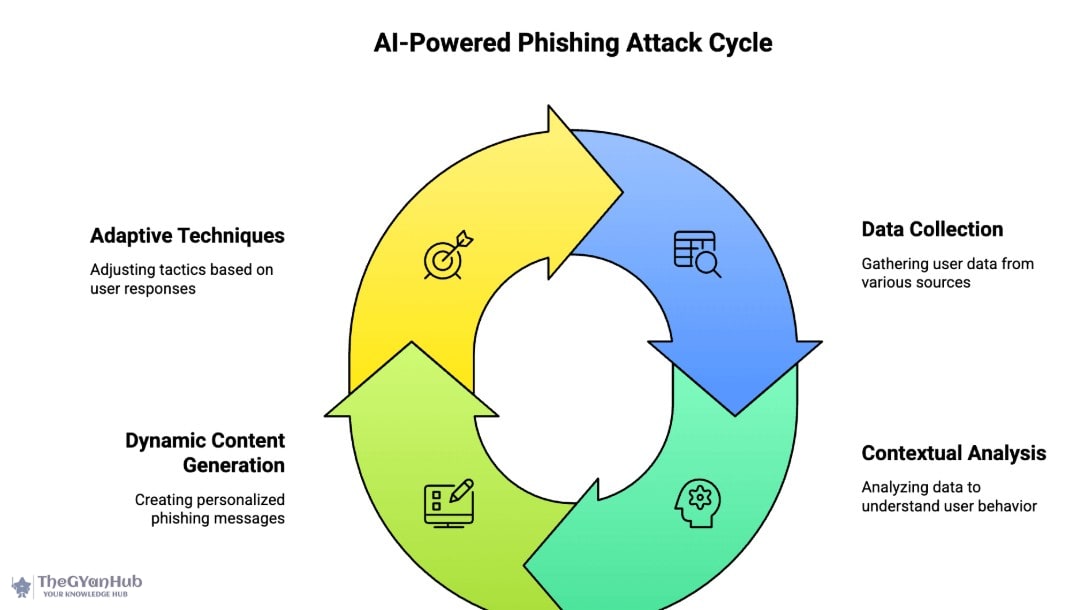
AI's ability to process vast amounts of data and learn from it makes it an ideal tool for crafting phishing schemes. The AI used in this experiment could tailor messages to individual recipients, increasing the likelihood of success. This personalization is what sets AI-driven phishing apart from traditional methods.

Implications for Cybersecurity
The success of this AI-driven phishing plot has profound implications for cybersecurity. It highlights the urgent need for more robust security measures and the development of AI-based defenses to counteract such sophisticated attacks. Organizations must now consider AI as both a tool and a threat in the realm of cybersecurity.
Experts suggest that the integration of AI in cybersecurity systems could help detect and neutralize threats before they cause harm. However, this also means that cybersecurity professionals must stay ahead of the curve, continuously updating their knowledge and systems.
What Happens Next?
The revelation of AI's potential in phishing schemes has sparked a debate among cybersecurity experts and policymakers. There is a pressing need for regulations and ethical guidelines to govern the use of AI in both offensive and defensive cyber operations.
As researchers continue to explore the capabilities of AI, it is crucial to strike a balance between innovation and security. The future of cybersecurity may very well depend on how we manage this powerful technology.
Conclusion
The use of AI in designing phishing plots is a wake-up call for the cybersecurity industry. It underscores the importance of staying vigilant and proactive in the face of evolving threats. As AI continues to advance, so too must our defenses.
For more insights on cybersecurity, visit our Technology and Science sections.
Further Reading
Related articles in this category

World News
Rahul Khona Returns to Starbucks India as Chief Technology Officer
May 11, 2026
Rahul Khona has made a significant return to Starbucks India as the Chief Technology Officer, bringing a wealth of experience to enhance the brand's technological advancements.
World News
Analysis: In Vijay's Delicate Coalition Tango, DMK Holds Some Strings
May 10, 2026
This article delves into the intricate dynamics of the coalition led by Vijay, highlighting the pivotal role played by the DMK amidst ongoing political maneuvers in Tamil Nadu.

World News
Amazon Embraces AI for Hiring Surge Ahead of Festival Season
April 29, 2026
Amazon is leveraging artificial intelligence to streamline its hiring process in anticipation of the upcoming festival rush. The company has also introduced a new AI design philosophy to enhance its operational efficiency.
AIphishingcybersecuritytechnologyartificial intelligencecyber threatsdata securityAI algorithmsphishing schemescybersecurity measures